How to Protect Your Digital Privacy at the US Border: A Step-by-Step Guide
Introduction
Traveling across the US border, whether by land, air, or sea, means you may face a search of your electronic devices—laptops, smartphones, tablets. The Electronic Frontier Foundation (EFF) is fighting to require a warrant for such searches, arguing before the 4th Circuit that they violate the Fourth Amendment. Until that becomes law, you need to know how to safeguard your data. This guide walks you through the legal landscape, preparation steps, and what to do if an officer demands access to your devices. It's based on the EFF's ongoing litigation and constitutional arguments.
What You Need
- Knowledge of your rights under the Fourth Amendment and border search exceptions
- A fully charged device with encryption enabled and strong passwords
- Cloud backup of critical files to avoid losing data if device is seized
- Contact information for legal aid organizations (EFF, ACLU)
- A notepad or voice recorder (where legal) to document encounters
- Patience and calm demeanor during interactions with border agents
Step-by-Step Guide
Step 1: Understand the Current Legal Situation
The Fourth Amendment protects against unreasonable searches and seizures. However, courts have long recognized a “border search exception” allowing warrantless searches of people and property entering the US. The EFF, in a brief to the 4th Circuit, argues this exception does not extend to the vast amount of personal data on electronic devices. The case centers on whether reasonable suspicion—or a warrant—is required. Under the EFF's view, a warrant must be obtained unless exigent circumstances exist. Travelers should be aware that the law is unsettled, so preparation is key.
Step 2: Know Your Rights at the Border
Currently, US Customs and Border Protection (CBP) and Immigration and Customs Enforcement (ICE) can search your device without a warrant at the border. They claim authority under the border search exception. However, the EFF contends that digital devices contain intimate private information far beyond any other container. You have the right to:
- Refuse to unlock your device — but be aware refusal may lead to detention or device seizure.
- Ask for a warrant — if they want to search, you can request they obtain a judicial warrant.
- Remain silent beyond providing basic identifying information required by law.
- Refuse to consent — if you do not consent, they need either a warrant or reasonable suspicion.
Note: The 4th Circuit case may change these rules. Stay informed via EFF updates.
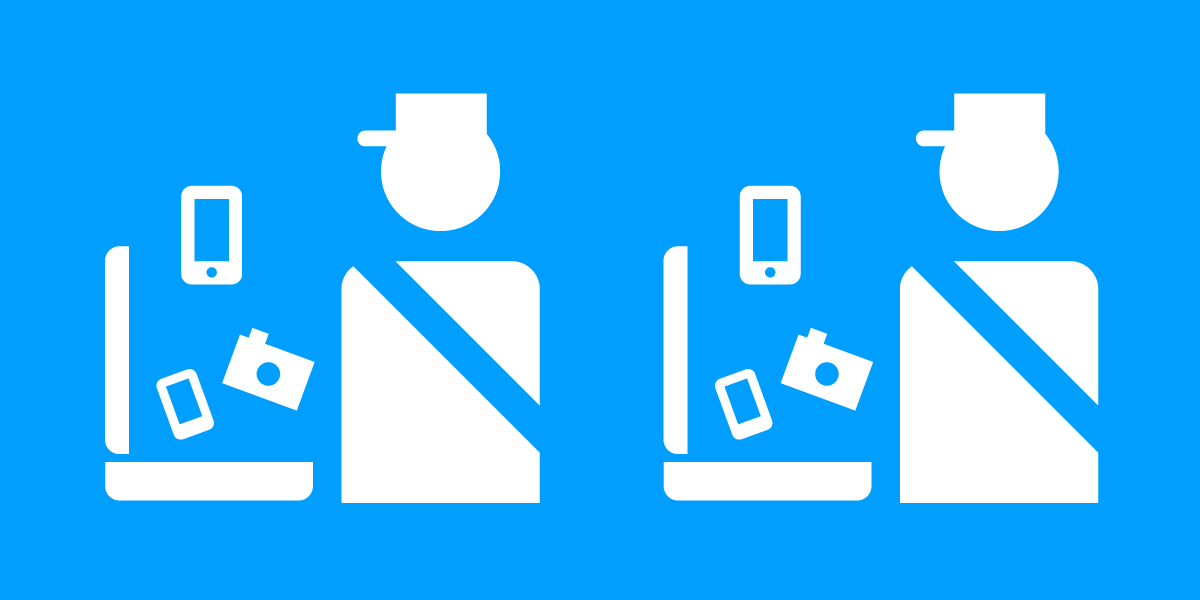
Step 3: Prepare Your Devices Before Travel
Take proactive steps to minimize exposure:
- Encrypt your device — Full-disk encryption on laptops and phone encryption (iPhone/iPad, Android) makes data unreadable without a passcode. Use a strong, alphanumeric password, not a simple PIN.
- Back up to the cloud — Before crossing, sync important documents offline and remove them from the device. You can restore later.
- Log out of accounts — Sign out of email, social media, and cloud storage. Use incognito or private browsing modes.
- Power off your device — When turned off, encrypted data is more secure. CBP may not be able to compel you to turn it on, though case law varies.
- Remove unnecessary data — Delete sensitive files that you don’t need for the trip. Use secure deletion tools.
- Use a “travel phone” — Consider a clean device with minimal data for crossing the border, then switch to your primary device later.
Step 4: Respond to a Search Request
If a border agent asks to search your device, follow these steps:
- Stay calm and polite. Do not argue, but clearly state: “I do not consent to a search of my device.”
- Ask if you are being detained. If they say no, you may be free to leave. If yes, ask for a lawyer.
- Do not provide your password or unlock your device. Saying “I decline to unlock” is better than providing access.
- If they seize your device, ask for a receipt and a reason. CBP must provide a record of seizure.
- Do not lie or destroy evidence. Do not delete files or attempt to erase data while they are watching. That can be obstruction.
- Request a warrant. You have a right to see a warrant before they search. If they claim reasonable suspicion, ask for that basis in writing.
Step 5: Document the Encounter
Gather evidence for potential legal action:

- Record the interaction — If local law allows, use a voice recorder or video. In many places, you can record CBP in a public area.
- Write down badge numbers, names, and agency details of all officers involved.
- Note the time, date, location, and duration of the encounter.
- Get witness information — if other travelers observed, ask for their contact.
- If device is searched or seized, note what was accessed or taken.
Step 6: Seek Legal Help
After the encounter, consider filing a complaint with CBP or contacting organizations like the EFF or ACLU. They track cases and may provide representation. Steps:
- File a CBP complaint online at their website.
- Contact the EFF via their intake page (eff.org) if your Fourth Amendment rights were violated.
- Hire a lawyer experienced in border search cases. The EFF may offer pro bono assistance.
- Share your story with advocacy groups to help change policy.
Tips and Conclusion
Tip 1: Travel with minimal data. More data means more risk. Use a cloud-only approach and download only what you need after crossing.
Tip 2: Use biometrics only if forced (e.g., face unlock) – but know that courts have split on whether you can be compelled to unlock with biometrics. A passcode offers more Fifth Amendment protection (you can’t be forced to reveal a password, but can be forced to use a fingerprint in some jurisdictions).
Tip 3: Keep your device in airplane mode when crossing. This prevents remote wiping by authorities if they demand you connect to their equipment.
Tip 4: Check the EFF’s “Border Search” guide for updates. Laws change rapidly.
Conclusion: The EFF’s push for warrant requirements is crucial. While the 4th Circuit case unfolds, you must take steps to protect your privacy. Preparedness, knowledge of rights, and a calm response can make a difference. Remember: you have the right to say no, but be ready for the consequences.
Related Articles
- The Ultimate Guide to Modern Device Charging: Steps to Upgrade Your Setup
- 10 Crucial Insights for Building a User-Centric Personalization Program
- Elle Prequel Series: Everything You Need to Know About the Legally Blonde Spin-Off
- Kubernetes v1.36 Haru: Spring Release Brings 70 Enhancements, Clear Skies for Cloud Native
- The Flame Malware Attack and Quantum Computing Threats: Lessons for Crypto Security
- Active Cooling Unlocks Sustained 80Gbps Speeds in the Satechi DotDisk SSD Enclosure
- Flame Malware Attack Warns Big Tech: Quantum Computing Threatens Cryptography
- Getting Started with Zhipu.AI's Open-Source GLM Models: A Developer's Guide