SPIFFE: The Identity Backbone for Autonomous AI and Non-Human Entities
Agentic AI systems—from autonomous drones to LLM-powered bots—operate beyond human supervision, making identity and trust a make-or-break factor. Traditional security models built for humans and static credentials fail in this dynamic world. Enter SPIFFE (Secure Production Identity Framework For Everyone), an open standard originally crafted for microservices but now essential for non-human actors. This Q&A explores how SPIFFE redefines identity for the age of autonomous agents.
What exactly is SPIFFE and how does it work?
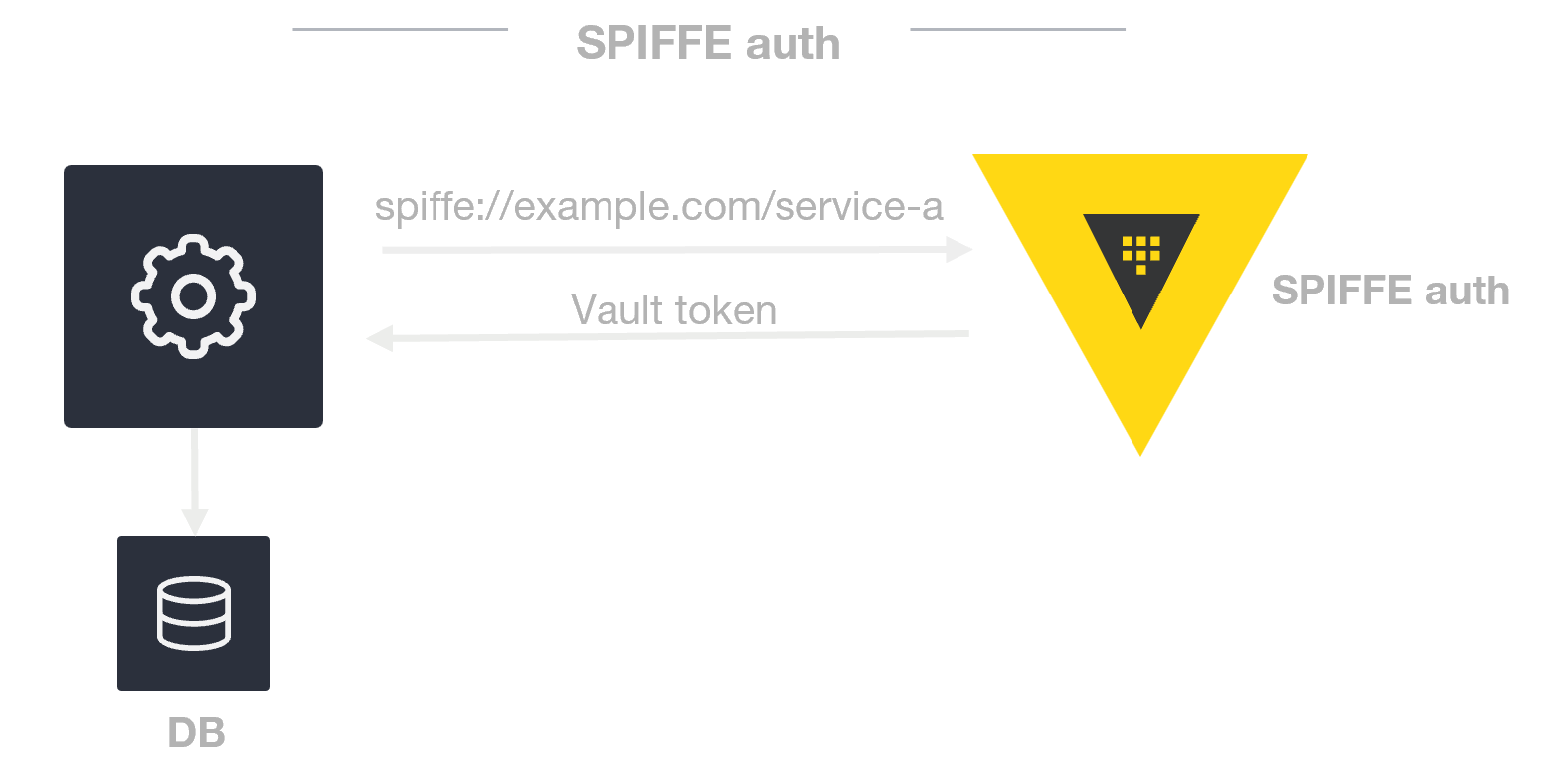
SPIFFE is an open standard that issues cryptographically verifiable identities to workloads or processes—not people. Instead of relying on long-lived secrets like passwords or API keys, each service gets a unique SPIFFE ID (e.g., spiffe://example.org/ai-agent/city-manager). These IDs are embedded in X.509 certificates and automatically rotated, so credentials stay short-lived and dynamic. At its core, SPIFFE enables three things: workload identity (every process has a unique ID), federated trust (IDs can be validated across different organizations), and dynamic credentialing (auto-issue and rotation). Think of it as a permanent, secure passport for software—perfect for non-human actors that need to prove who they are in zero-trust environments.
Why does SPIFFE matter for agentic AI systems?
Autonomous AI agents—like bots managing smart grids or robotic vacuum cleaners—often operate in multi-agent ecosystems. They need to prove their identity to each other, establish trust, and communicate securely across networks. SPIFFE addresses these needs directly. First, it provides verifiable non-human identity: SPIFFE IDs are tied to workloads, not people, so each agent can prove its origin and capabilities. Second, it supports zero trust architecture via mutual TLS, ensuring every interaction is authenticated and encrypted. Third, its federation model allows identities to be validated across clouds and organizations—crucial for AI systems that span multiple environments. Finally, the dynamic identity lifecycle matches the ephemeral nature of many AI agents: certificates are automatically rotated and revoked, reducing the attack surface. Without SPIFFE, managing trust for thousands of short-lived, independent AI agents becomes a security nightmare.
How does SPIFFE provide verifiable identity for non-human actors?
Traditional identity frameworks assume a human user—complete with passwords or biometrics. But non-human actors like AI agents, robotic systems, or serverless functions need a different approach. SPIFFE solves this by binding identity to the workload itself. Each agent receives a cryptographically signed SPIFFE ID that proves its provenance (e.g., which organization issued it and its trust level). The ID is embedded in an X.509 certificate, which is automatically renewed and can be instantly revoked. For example, a traffic-management AI agent might hold the SPIFFE ID spiffe://city-smart.ai/traffic-agent-72. When another agent (say, a power-grid manager) receives this ID, it can verify the signature against a trusted root. This eliminates the need for shared secrets or API keys—credentials that can be stolen or leaked. It also makes identity machine-readable and scalable, perfect for environments where thousands of agents are constantly being created and destroyed.
How does SPIFFE support zero trust architecture for AI agents?
Zero trust assumes that no entity—inside or outside the network—is trustworthy by default. Every request must be authenticated, authorized, and encrypted. SPIFFE enables this through mutual TLS (mTLS). Each agent presents its SPIFFE-issued certificate when connecting to another agent. The receiving agent validates the certificate against its trust bundle (a list of trusted certificate authorities), confirming the sender’s identity and that its certificate hasn’t been revoked. Once validated, an encrypted channel is established. This prevents impersonation attacks: a malicious script can’t pretend to be the traffic agent without its private key. Furthermore, SPIFFE allows fine-grained authorization policies based on the SPIFFE ID—e.g., “only allow agents with IDs starting with spiffe://city-smart.ai/traffic to modify traffic light states.” This granular control is vital for agentic AI where actions have real-world consequences.
How does SPIFFE federation enable multi-domain agent collaboration?
Agentic AI systems rarely live in a single cloud or organization. A smart city might have agents running on Azure (managing energy) and on-premises servers (handling traffic). Each operates in its own trust domain—a boundary where identities are managed by a local SPIFFE authority. To allow secure cross-domain communication, SPIFFE supports federation. Domain A publishes its trust bundle (root certificates), and Domain B imports it—or vice versa. When an agent from Domain A (e.g., spiffe://azure-city.ai/energy-agent) contacts an agent in Domain B (e.g., spiffe://onprem-city.traffic-helper), both sides validate each other’s certificates using the imported trust bundles. This eliminates the need for a shared central authority. The federation model is decentralized and scalable, ideal for AI ecosystems that cross organizational boundaries, such as autonomous vehicle fleets from different manufacturers or disaster-response robots from multiple agencies.
What is a dynamic identity lifecycle and why does it matter for short-lived AI agents?
AI agents are often ephemeral—spun up to handle a burst of tasks then decommissioned. In a factory, dozens of inspection drones might be launched, finish scanning, and return to base in minutes. Traditional static credentials (like API keys) would be impractical: rotating them manually breaks automation, and long-lived keys increase the risk of theft. SPIFFE’s dynamic identity lifecycle automates certificate issuance and rotation. A SPIFFE Workload API running on the host provides certificates on-demand. When a new agent starts, it requests a SPIFFE ID; the Workload API issues a short-lived certificate (e.g., valid for 1 hour). The agent uses that certificate for all mTLS connections. Before expiry, the agent asks for a new one—no human intervention required. Revocation is also instantaneous: if an agent is compromised, its certificate can be revoked, and future connections are rejected. This agility reduces the attack surface and keeps pace with the rapid churn of agentic AI.
Can you walk through a real-world use case of SPIFFE for AI agents?
Consider a smart city deploying a swarm of autonomous agents to manage traffic, energy grids, and emergency response. Each agent has a unique SPIFFE ID: spiffe://city-smart.ai/traffic/t12, spiffe://city-smart.ai/energy/e9, spiffe://city-smart.ai/emergency/ambulance-3. When the traffic agent wants to request a green wave for an ambulance, it initiates an mTLS connection to the ambulance agent. Both agents verify each other’s SPIFFE certificates, ensuring they’re legitimate city-managed entities. The ambulance agent checks the traffic agent’s authorization—can it request route changes? The policy engine confirms based on the SPIFFE ID suffix. All data exchanged (e.g., location, velocity) is encrypted. If the traffic agent is compromised, its certificate is revoked, and no other agent will trust it. The entire process is automated and handles thousands of interactions per second. SPIFFE gives the city a scalable, zero-trust identity layer that works across different hardware and cloud providers.
Related Articles
- A Step-by-Step Guide to Quantum Processor Calibration Using NVIDIA Ising Open Models
- MOREFINE G2 eGPU Dock: Is the RTX 5060Ti Worth $1099?
- Building Trust for Autonomous AI: How SPIFFE Creates Secure Identities for Non-Human Agents
- Unlocking Your Android's True RAM Potential: Fix App Reloads and Stutters on 12GB Devices
- 8 Things You Need to Know About SPIFFE for Agentic AI Identity Security
- How the FPGA Revolutionized Hardware Flexibility: A Guide to Reconfigurable Computing
- Intel's Unified Chip Strategy Shines at Computex 2026: A Decade in the Making
- NVIDIA Engineers Tackle CPPC v4 Support for Linux ACPI Driver – A Leap Forward in Core Performance Management