How UK Policymakers Can Protect Children Online Without Breaking the Internet
Introduction
Online safety for children is a pressing concern, but recent UK proposals risk doing more harm than good. Instead of imposing sweeping age-gating and access restrictions that threaten the open web, policymakers can take a more effective, rights-respecting approach. This guide outlines step-by-step how to address the roots of online harm—focusing on platform accountability, user empowerment, and preserving the internet’s global, accessible nature.
What You Need
- Understanding of current proposals – Familiarize yourself with the Children’s Wellbeing and Schools Bill and the age-assurance measures being considered.
- Commitment to rights-respecting policies – A willingness to prioritize privacy, anonymity, and freedom of expression while tackling harm.
- Data on platform business models – Insights into how engagement-driven design and data collection contribute to harm.
- Stakeholder input – Perspectives from civil rights groups (e.g., EFF, Mozilla), technologists, youth advocates, and affected users.
- Legal and technical expertise – Collaboration with experts who understand the internet’s architecture, privacy-preserving alternatives, and regulatory frameworks.
Step-by-Step Guide
Step 1: Analyze the Root Causes of Online Harm
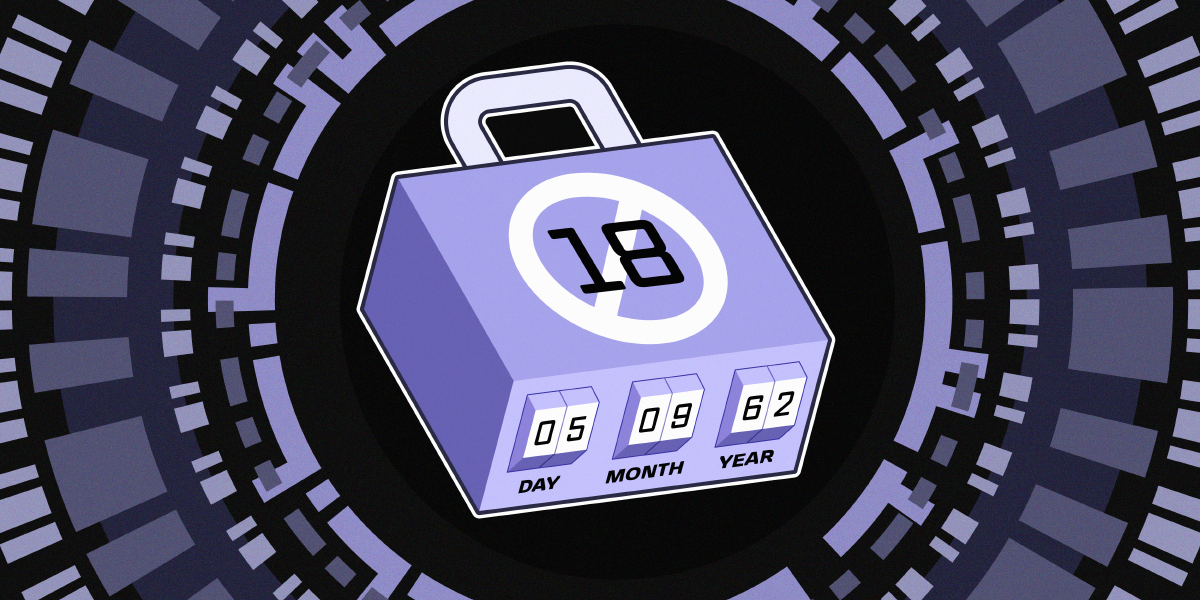
Before designing any intervention, policymakers must understand what drives harm. The letter from EFF and 18 organizations (including Mozilla and the Tor Project) points to platform design choices—maximizing engagement through pervasive data collection, targeted advertising, and addictive features—as primary factors. These practices often exploit users, especially children, without regard for safety. Conduct a thorough review of the most harmful services, focusing on:
- How data monetization fuels misinformation, bullying, and exploitation.
- How algorithmic amplification escalates risks.
- How default privacy settings and consent mechanisms fail users.
Step 2: Reject Blanket Age-Gating and Access Restrictions
The coalition warns that proposals to mandate age verification across social media, video games, VPNs, and basic websites are inaccurate, privacy-invasive, and counterproductive. Such measures would require all users to prove identity merely to access the web, expanding surveillance and increasing breach risks. Instead:
- Promote context-specific, privacy-preserving age assurance (e.g., local, anonymized checks) only where essential.
- Resist broad requirements that fragment the internet into restricted zones or entrench gatekeepers like app stores.
Step 3: Hold Platforms Accountable for Systemic Practices
Rather than restricting access, focus on the practices that generate harm. The letter calls for holding companies accountable for design choices and business models that prioritize profit over safety. Key actions include:
- Mandate privacy-by-default and safety-by-design for all platforms.
- Require transparency reports on algorithmic impacts and data use.
- Enforce meaningful penalties for companies that repeatedly harm users, especially children.
Step 4: Preserve the Open Web’s Core Qualities
The internet’s power lies in its interoperability, accessibility, and openness. The letter emphasizes that age-gating at scale would fragment the web, limit information access, and empower dominant gatekeepers. Policymakers should:

- Ensure any regulation does not weaken encryption or anonymity.
- Protect end-to-end encryption and private communication.
- Support decentralized, open standards instead of walled gardens.
Step 5: Empower Young People Through Positive Access
The internet remains a vital space for youth—offering information, support networks, and expression not available offline. Blanket restrictions cut off these lifelines without reducing harm. Instead:
- Invest in digital literacy education to help children navigate risks.
- Fund noncommercial safe spaces for youth interaction.
- Promote user agency—tools that let children control their own privacy and content filters.
Step 6: Engage with Diverse Stakeholders
Effective policy emerges from collaboration. The coalition includes Mozilla, EFF, Open Rights Group, and others. Policymakers should:
- Consult civil liberties organizations and technical experts on feasibility and rights implications.
- Include youth voices to understand their experiences and needs.
- Pilot targeted interventions before scaling to avoid unintended damage.
Tips for Success
- Avoid silver-bullet solutions – No single technology or restriction can solve online harm; combine several rights-respecting measures.
- Prioritize privacy – Any policy that weakens encryption or anonymity increases overall vulnerability, especially for children.
- Think globally – The internet has no borders; UK policy should avoid isolating the nation or fragmenting the global web.
- Learn from other countries – Examine approaches like the EU’s Digital Services Act that balance safety with openness.
- Monitor and adapt – Regularly evaluate the impact of measures on harm reduction and internet freedom, adjusting as needed.
Conclusion
Protecting children online requires more than heavy-handed restrictions. By tackling the business models behind harm, preserving the open web’s architecture, and empowering users, UK policymakers can create a safer internet without sacrificing its fundamental qualities. The letter from EFF and coalition partners provides a roadmap: thoughtful, rights-respecting policies that truly address the roots of online harm.
Related Articles
- Visual Studio Code Python Extension: Key Updates in March 2026
- How to Become a Member of the Python Security Response Team
- Python 3.14.0 Officially Released: Free-Threaded Python and Deferred Annotations Lead Major Update
- 10 Critical Lessons from the SAP npm Package Attack on Developer Tools and CI/CD Pipelines
- 10 Ways Go Optimizes Performance with Stack Allocation
- Mastering Automated Testing: A Guide to Python's unittest Module
- Spotify Unveils Conversational Ads API Interface Powered by Claude AI — No Code Required
- Python Security Response Team Gains Formal Governance and First New Member in Two Years